Challenge Description
A photograph was recovered during an investigation.
At first glance, the image appears completely unrelated to any specific location. However, digital files often contain hidden information embedded within their metadata.
Your mission is to analyze the image file and determine the real-world location referenced in the hidden message.
To Get Started:
- Download the folder
- Unzip the folder
- Enter the password “osintchallenges.com”
- Start investigating
Download Challenge File

A packet capture file has been recovered from a user’s browsing session.
The capture contains several normal website visits followed by one final destination.
Your mission is to analyze the network traffic and determine which domain the user accessed last.
This challenge focuses on network analysis fundamentals, including DNS inspection and traffic interpretation using packet capture data.
Getting Started
- Download the challenge file using the button above.
- Extract the ZIP archive using the password:
osintchallenges
- Open the extracted PCAP file in Wireshark.
- Inspect the captured traffic and submit your answer below.

A publicly accessible website is running a specific content management system (CMS).
Your mission is to analyze the target website and determine which CMS powers the site.
Target: https://www.tesla.com

The container vessel shown below was observed operating in U.S. waters.
Using open-source maritime tracking data, your mission is to determine the date on which this vessel arrived at Port Houston, United States.
This challenge focuses on transportation OSINT, including vessel identification, voyage history analysis, and AIS-based tracking.
Objectives
- Identify the vessel shown in the image
- Analyze maritime tracking data for the vessel
- Determine the arrival date at Port Houston, United States
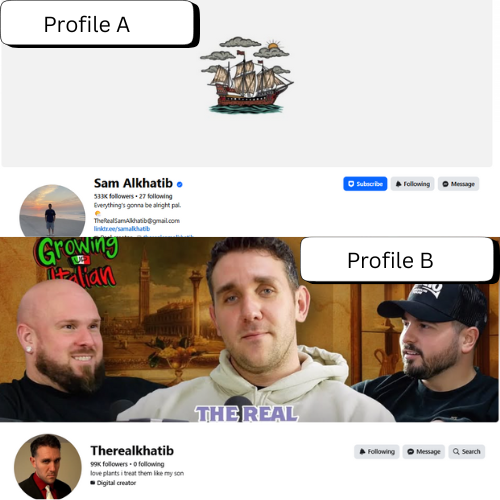
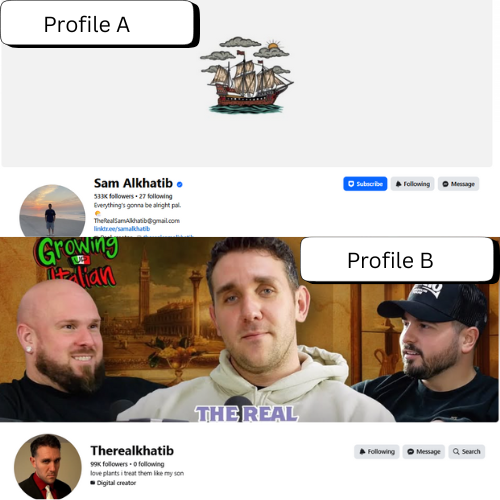
Two social media profiles appear to represent the same online personality.
At first glance, both accounts look legitimate.
However, one of these profiles is an impersonation account.
Your mission is to analyze both profiles and determine which profile is being impersonated.
This challenge focuses on SOCMINT techniques, including profile verification, branding consistency, and cross-platform correlation.
Objectives
- Analyze Profile A and Profile B
- Compare profile details, imagery, and branding
- Determine which profile is the impersonated account

Challenge Description
An unusual photo circulated online showing a group of people having drinks inside a bar — but no location metadata was attached.
Your mission is to identify:
- The name of the establishment
- The city
- The state
- The country
- The year the image was captured
This challenge focuses on visual GEOINT, environmental clues, and open-source research.

The Bitcoin address below is widely known as a tribute address associated with Satoshi Nakamoto and continues to receive small transactions from the public.
On January 6th, 2026, a transaction was broadcast to this address and included in the Bitcoin blockchain.
Your mission is to analyze the transaction and determine exactly how much BTC was received in that specific transaction.
Address:
1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa
Transaction Hash:
d8773c23582a0bf0fe7f640fd1053c14c5ebf3782fed994bd9cd2aed7d19dedd
Objectives
- Locate the transaction using the provided transaction hash
- Identify the recipient address
- Determine the exact amount of BTC received in the transaction